Cybersecurity in the AI Era: Risk, Resilience, and Reality (feat. Alex Lanstein)
AI is transforming cybersecurity by accelerating both defense and attack capabilities. While automation improves threat detection and code security, it also empowers adversaries.
Artificial intelligence is not merely influencing cybersecurity — it is redefining it. What was once a battle of firewalls and antivirus software has become an intelligence war between automated defenders and increasingly automated attackers. As discussed in the Snowpal podcast conversation with Alex Lanstein, CTO of StrikeReady , the landscape has evolved from spam botnets and early cybercrime to highly targeted, state-sponsored, and supply-chain-level attacks. Today, AI accelerates both sides of the battlefield.
Podcast
AI and Cybersecurity: The Escalating Intelligence War - on Apple and Spotify.
The Security Operations Center: Same Mission, Greater Complexity
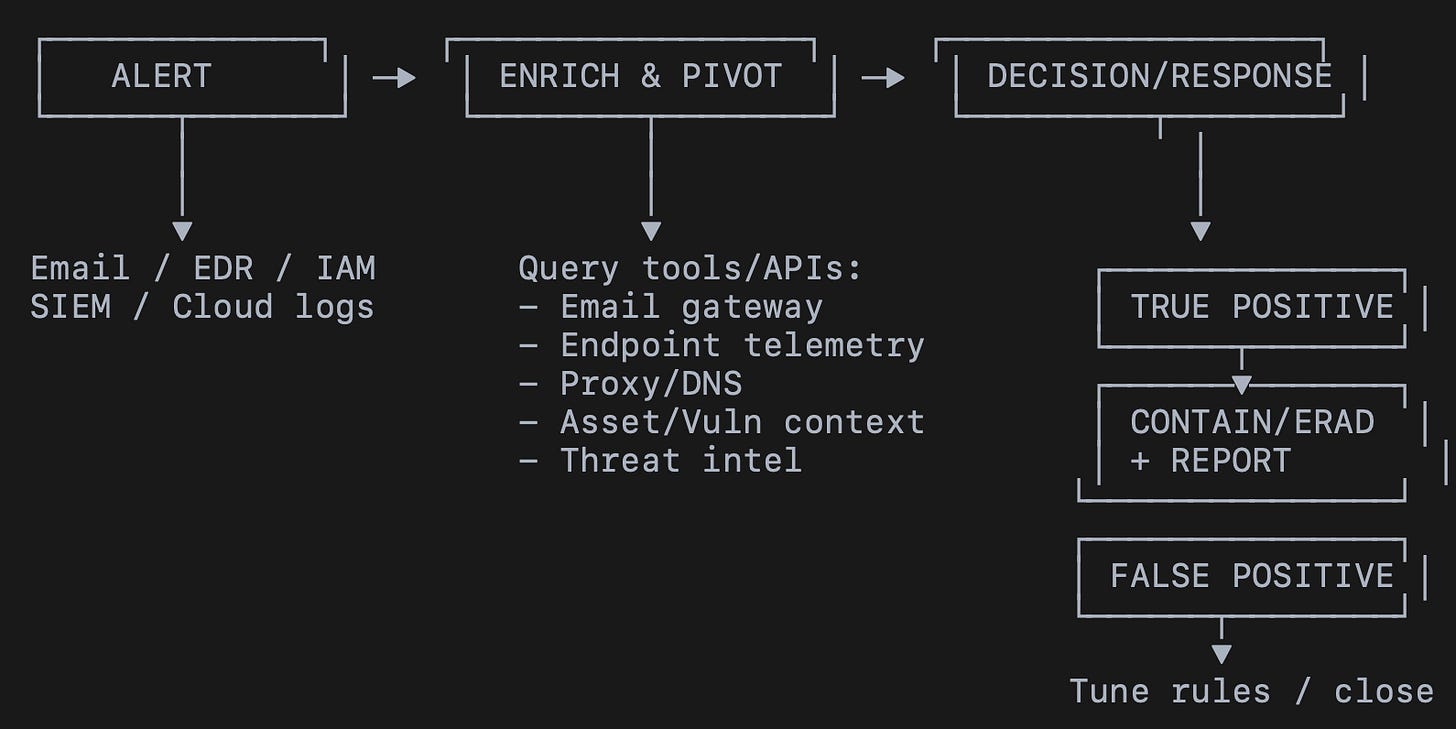
At its core, the work of a Security Operations Center (SOC) has not fundamentally changed in 15 years. When an alert is triggered, analysts still ask the same foundational questions:
Is the alert legitimate?
Did the user interact with it?
Has the threat spread?
Who else might be impacted?
What has changed is scale, speed, and fragmentation. Modern enterprises operate dozens of security tools across email, endpoints, identity systems, cloud infrastructure, and web gateways. Historically, analysts manually logged into multiple consoles, ran queries, copied outputs into spreadsheets, and stitched together investigations. Integrations were brittle. APIs were inconsistent. Runbooks were manual.
Today, automation and AI-driven orchestration are finally enabling centralized triage. Alerts can be enriched with identity context, vulnerability data, and asset information in near real-time. The SOC is shifting from reactive manual labor toward intelligent, automated investigation pipelines.
The Expanding Threat Surface
Cybersecurity threats are no longer confined to phishing emails. They exist across multiple dimensions:
Social Engineering and Credential Abuse
Attackers steal usernames and passwords through phishing, then bypass multi-factor authentication using techniques like voice impersonation or MFA fatigue attacks. Even secure authentication systems can be socially engineered.
Insider Threats
Not all breaches originate externally. Malicious insiders — or compromised employees — can abuse legitimate access. Detecting insider misuse is difficult because the activity often appears operationally valid.
Software and Supply Chain Vulnerabilities
Organizations inherit vulnerabilities not only from their own code but also from open-source libraries and third-party dependencies. Compromised packages and backdoored libraries can silently propagate into thousands of systems before detection.
Edge Device Exploitation
An increasingly dangerous category involves vulnerabilities in VPN concentrators, firewalls, SSL appliances, and email gateways. These devices sit at the network perimeter and often do not allow endpoint detection agents to be installed. As a result, attackers can compromise them with minimal visibility from security teams.
The attack surface continues to widen as organizations adopt cloud services, APIs, SaaS integrations, and distributed work environments.
Reasonable vs. Unreasonable Threats
No organization can defend against every conceivable attack. Security leaders must make trade-offs between protecting against high-frequency threats and preparing for rare, highly sophisticated adversaries.
Most organizations face constant probing from automated ransomware campaigns and botnets. These are not necessarily targeted, but they can still cause catastrophic disruption. On the other end of the spectrum are nation-state-level supply chain attacks — rare but extremely damaging.
The solution is layered defense:
Prevent common attacks.
Detect what bypasses prevention.
Limit lateral movement.
Protect crown-jewel data.
Detect data exfiltration.
Recover effectively.
Security is not binary. It is probabilistic and strategic.
The Technology Shift: APIs, Automation, and AI-Driven Security
Technology has matured significantly in recent years. Security vendors now expose stable APIs that allow organizations to automate investigations across systems. What once required manual integration and brittle scripts can now be orchestrated through middleware layers and security automation platforms.
AI and large language models (LLMs) are becoming force multipliers within this ecosystem. They can:
Correlate signals across multiple tools
Summarize alert data in seconds
Identify anomalous patterns across identity logs
Detect insecure code logic
Reduce false positives in code scanning
In software development, AI-powered static analysis tools can review vast codebases and detect vulnerabilities with far greater accuracy than previous generation scanners. These models are trained on enormous corpora of insecure code and publicly documented exploits, allowing them to recognize patterns that human reviewers may miss.
However, the same AI models that enhance defensive capabilities also accelerate vulnerability discovery. Legacy systems that have not been audited in years can now be scanned and analyzed at unprecedented speed. As a result, we may see an explosion of newly identified vulnerabilities — not because they are new, but because AI makes them easier to find.
AI as a Defensive Multiplier
In today’s SOC, AI frees analysts from low-level triage work. Many organizations generate large volumes of medium- or low-severity alerts that are often ignored due to resource constraints. AI systems can automatically enrich, investigate, and summarize these alerts, enabling human analysts to focus on deeper anomaly detection.
In effect, AI elevates human capability. A junior analyst can operate at a far higher level of effectiveness with AI augmentation. Investigations that once took hours can now be completed in minutes.
This does not eliminate the need for cybersecurity professionals. Instead, it shifts their focus toward strategic analysis, adversary modeling, and resilience planning.
AI as an Offensive Accelerator
The more alarming transformation is on the offensive side. AI dramatically reduces the cost and time required to launch sophisticated attacks.
An attacker can now:
Scrape public data about a target
Generate personalized phishing emails
Simulate months-long email conversations
Create malicious documents automatically
Automate infrastructure deployment
Previously, such targeting required manual research and setup. Now it can be automated at scale. Social engineering becomes more believable. Reconnaissance becomes instant. Attack campaigns become scalable.
The barrier to entry has dropped. Sophisticated tactics are no longer exclusive to elite adversaries.
The Human Factor: The Most Persistent Vulnerability
Technology is only part of the equation. Seniors are increasingly targeted by AI-enhanced scams, including deepfake voice impersonation. The financial and emotional damage can be devastating.
Children and teenagers face exploitation across social platforms where billions of users make monitoring extremely difficult. Unlike financial fraud, these harms often have long-term psychological consequences.
There is no simple technical fix. Monitoring tools, education, and stronger platform governance are necessary — but the challenge is deeply societal as well as technological.
Security vs. Usability: A Global Perspective
Different regions adopt different approaches to balancing security and convenience. In some countries, banking transactions require multiple authentication steps, dual approvals, and strict timing windows. These measures may feel excessive but significantly reduce fraud liability.
In the United States, consumer protection laws and fraud absorption by financial institutions allow for simpler user experiences. The design philosophy often depends on who bears the financial risk when fraud occurs.
Security architecture is shaped as much by economics and liability frameworks as by engineering capability.
The Future: Intelligent Resilience
AI will not eliminate cybersecurity roles. It will increase the need for strategic thinkers who can interpret signals, model adversaries, and design layered defenses. Attack sophistication and volume are rising. AI empowers defenders — but it equally empowers attackers.
The future of cybersecurity lies in adaptive digital immune systems that:
Continuously learn from telemetry
Detect subtle anomalies
Contain breaches quickly
Recover without catastrophic disruption
Breaches are inevitable. Intelligent resilience is the goal.
Artificial intelligence is not a silver bullet. It is an accelerant. It amplifies strengths and weaknesses alike. The organizations that thrive will not be those that attempt to eliminate risk entirely, but those that build intelligent systems capable of surviving in an increasingly automated threat landscape.